stSoftware blog

How are server issues (faults etc) monitored?
19 Mar 2014
We have automated heart beat monitors which checks the health of the servers and a number of background tasks. In addition to checking the list of known tasks database read & write actions are performed and the available disk space is checked. If the heart beat monitor itself takes more than 5 minutes to run an alert is sent. The heart beat monitor runs every 15 minutes. The list of tasks that the system will monitor are defined in the class DBTask. A task is defined by:- code which uniquely identifies...
Read More
How are SQL Injection attacks prevented?
14 Mar 2014
SQL injection is a code injection technique, used to attack data driven applications like stSoftware. stSoftware systems support a number of web accessible protocols including:- ReST SOAP Web Forms GWT RPC All protocols access the underlying data through the DAL ( data access layer). There is NO direct access to the underlying data store no matter which protocol is used. Each protocol accepts the request to read or write data and then perform the protocols validations and then passes the request...
Read More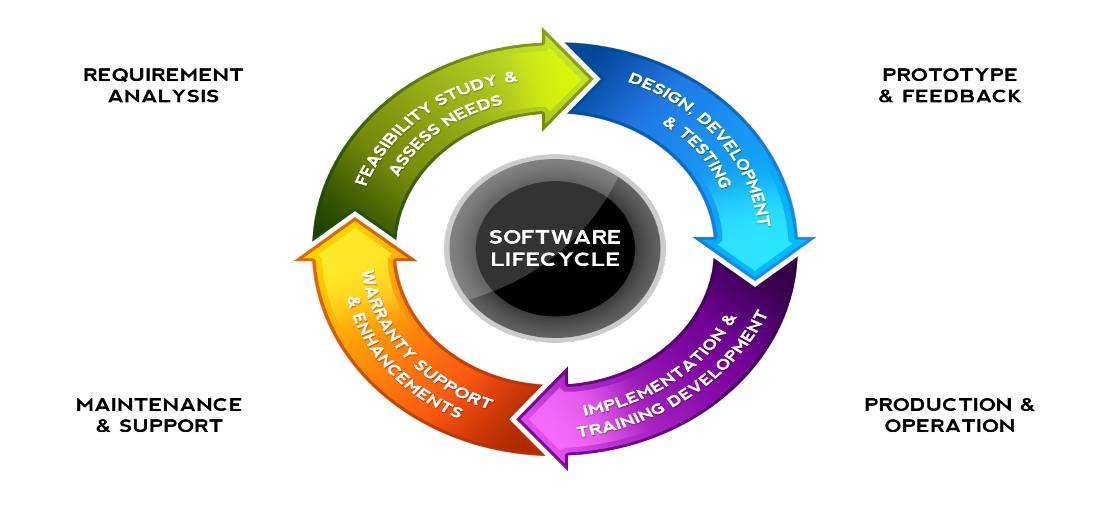
What is the recommended upgrade schedule for self hosted systems?
4 Mar 2014
We recommend at least quarterly maintenance release are installed to your test environment, tested then promoted to your production system as part of the normal software maintenance cycle. Regular and timely updates reduce the risks of running a live system that is out of sync with stSoftware's current version and enables your users to benefit from our R&D program, which is our investment and commitment to continually improve our systems for our customers (in recent years we have typically invested...
Read More
Windows Active Directory Single Sign-on for stSoftware servers
2 Mar 2014
Overview Single sign using Microsoft LAN Manager (NTLM) allows users within a intranet enviroment to use the system without the need to re-enter their password once they have logged into the Windows network. Note the NTLM protocol can only be used within a internet environment. Configuration Within a Windows intranet environment . Multiple options available within the The system has a environment variable “SSO_DISABLE” which can be used to completely disable Single Sign On for a server. Each layer... * * If disabled at the * Signal Sign On modes * 1) TRANSPARENT - only transparent login * 2) HYBRID - Transparent or database password. * * @param layer the layer * @param userModeSSO user wants to enable SSO * @return true if enabled. * @throws Exception a serious problem. */ public static String ssoMode( final VirtualDB layer, final String userModeSSO) throws Exception { DBSysPrefs sysPrefs = layer.getGlobalObject().getSysPrefs(); String ssoDisable= sysPrefs.getString( DBSysPrefs.DBFIELD_SSO_DISABLE); if( "yes".equalsIgnoreCase(ssoDisable) || "true".equalsIgnoreCase(ssoDisable)) { return ""; } if( MODE_HYBRID.equalsIgnoreCase(userModeSSO) ) { return MODE_HYBRID; } else if( MODE_TRANSPARENT.equalsIgnoreCase(userModeSSO) ) { return MODE_TRANSPARENT; } else if( "false".equalsIgnoreCase(userModeSSO) ) { return ""; } else if( StringUtilities.isBlank(userModeSSO) == false) { LOGGER.warn("invalid SSO user mode: " + userModeSSO ); } String layerModeSSO= sysPrefs.getString( DBSysPrefs.DBFIELD_SSO_MODE); if( MODE_HYBRID.equalsIgnoreCase(layerModeSSO) ) { return MODE_HYBRID; } else if( MODE_TRANSPARENT.equalsIgnoreCase(layerModeSSO) ) { return MODE_TRANSPARENT; } else if( StringUtilities.isBlank(layerModeSSO) == false) { LOGGER.warn("invalid SSO layer mode: " + layerModeSSO ); } return ""; } If the SSO mode is calculated to be “HYBRID” then the user's browser will be redirected to a protected page on the IIS server. The protected page on the IIS server will cause the user to authenticated via NTML. Once the user is authenticated the user details are encrypted with a private key known as a “shared secret” and then these encrypted details are re-directed back to the calling webserver. The calling webserver decrypts the user details using the “shared secret” private key. If the authentication...
Read More
Site Wizard can create a professional site in minutes.
26 Feb 2014
Our site wizard is a simple way to get a professional website Simply click on the wizard, enter your company details into the form provided and your information will automatically populate the pre-designed website template of your choice, giving you a quality website in minutes. You can choose to use this website, change the template, or tweak it to your hearts content, our system is accommodating and easy to use. There are a number of pre-designed site templates included in the base system. Open...
Read More
How to dynamically resize images on the server side?
31 Jan 2014
Overview The download of large images to the client browser which will be later resized to be a smaller image is very wasteful and slow. Let the server dynamically resize and cache your images with NO overhead to subsequent calls. To use in your HTML just add the desired behaviour to the URL e.g "?max-width=100" Available image transformations The sample large image is a landscape image of 1,000px × 667px which is 1.1m in size. You can resize the image while maintaining the same aspect ratio. The...
Read More
What is the recommended configuration for a Linux server?
26 Jan 2014
Overview All Linux servers are locked down to the highest security standards possible. All services are off by default and all ports shut. Only the required services started. To lock down a server:- Install and run only the services you require. Block all ports by default and open only those that are required Run servers as low permission user Disable direct login to ROOT completely. Block SSH login attempts from unknown locations and machines. Set up tripwire to detect intrusions Increase file ... sudo ufw allow imap sudo ufw allow http sudo ufw allow https sudo ufw disable sudo ufw enable Redirect the high permission ports 80 (http) and 443 (https) up to a port range that can accessed by the low permission user running the web service. Redirection of the ports can be done by the following iptable rules -A PREROUTING -p tcp -m tcp --dport 80 -j REDIRECT --to-ports 8080 -A PREROUTING -p tcp -m tcp --dport 443 -j REDIRECT --to-ports 8443 Create low permission user to run the web server Avoid running any custom code or the web server as a high permission user. A security...
Read More
Page Keywords Meta Tag
8 Jan 2014
The "keywords" meta tags is no longer used by any of the major search engines. Under some circumstances they can actually be scored negatively against the page rank, when a high count of irrelevant or duplicated key words are added. The system will automatically de-duplicate keywords if entered. For example if "SEO, meta, Seo,tags,,," is entered as the list of keywords, the list will be converted to "SEO, meta, tags" Later releases will deprecate the entry of key words completely. Currently Google...
Read More
Assigning a domain (host) name to your stSoftware hosted website or web system
1 Jan 2014
After you have registered a new domain name with a domain name (DNS) provider such goDaddy, or you have an exisiting domain name, you need to change the associated IP address so that your domain name points to stSoftware's servers. Or contact us to add "Assigning your domain name" service to your website or websystem package and we'll manage it for you. Assign your domain (host) name to the IP addresses of our servers Have your DNS pointed to either of the two groupings of IP addresses below; 101...
Read More
How to configure DNS round robin for web server failover?
18 Dec 2013
Server Cluster A cluster of servers (two or more ) can be setup and the DNS entry for your site can be defined with the IP addresses for each of the servers, this is known as Round-robin DNS DNS round-robin for Web server failover www1 -> 10.0.0.1 www2 -> 10.0.0.2 www -> 10.0.0.1, 10.0.0.2 Now the DNS server returns both IP addresses for each www query, in random order. If both web servers are up, obviously no problem. If one is down. the questions are, will the browser try the second IP address...
Read More
Social features are integrated into the core of the CMS
14 Dec 2013
When articles are published the built in social integration automatically posts the article to the requested social sites. When posting to twitter the title and subtitle are automatically shorten to within the 140 character limit. All published articles are automatically published via the RSS feed. The CMS automatically generates an XML Sitemap which can be submitted to search engines for faster indexing of new content.
Read More
Reporting facilities
13 Dec 2013
There are many built in reports created in the screen painter. Jasper Reports can be designed and uploaded for more complex reports External tools such as Open Office or Excel can be used to generate reports via JDBC or ReST web services.
Read More
What are the supported browsers?
13 Dec 2013
Supported desktop browsers Chrome Firefox Safari Internet Explorer Supported tablets iPad 2+ with iOS7+ Android tables 4.3+ Supported mobiles iPhone iOS7+ Android Phones 4.3+ Ever Green browsers We support the latest version of Google Chrome and FireFox (which automatically updates whenever it detects that a new version of the browser is available). We support the current and previous major releases of Safari on a rolling basis. Each time a new version is released, we begin supporting that version...
Read More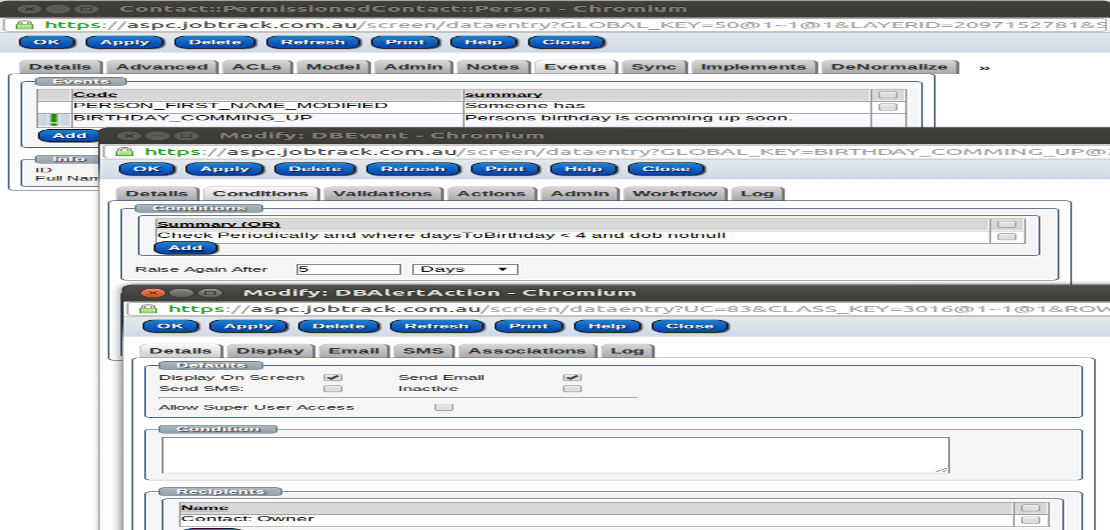
Is workflow customizable?
13 Dec 2013
Workflow is a series of activities that form a real world process and defines the order in which these activities are processed and their dependencies. In a software sense, ' work flow' refers to the triggering of events and the processing of corresponding actions. This process turns a software application from being simply a data entry and retrieval system into a business application that reflects business processes, thus increasing both quality and productivity and reducing costs. Events Triggers...
Read More
System security overview
13 Dec 2013
Overview stSoftware designs systems to meet or exceed all aspects of the Australian Government Protective Security Policy Framework PSPF. At stSoftware, we take security very seriously. Our ephemeral workload servers are locked down to be accessed only via bastion hosts; the support team can only access the bastion hosts themselves via secure shell from specific IP addresses. stSoftware follows Infrastructure as Code principles for all AWS services. Network design Best practice network design for...
Read More
Does the CMS include a script manager?
5 Dec 2013
Every page can define a script and/or include a number of script modules. Each script module can have many versions of the JavaScript. Each script version can specify what is the maximum and/or minimum browser version compatible with this script. The page can specify the a maximum version number for inclusion or just the script module. The script manager will include the highest compatible script version.
Read More
User Access Control Limits
5 Dec 2013
Every class in the system has ACLs (Access Control Limits ) which prevent CRUD ( Create, Read, Update and Delete) of records that are unauthorized. These ACLs are applied to all requests regardless of where or how the requests is made. The same ACLs apply to web forms, SOAP requests, ReST or any other protocol.
Read MoreHow to manage the site structure?
5 Dec 2013
Each site has a series of pages and menus. A page can be taken offline or scheduled to be taken on/off line at a certain time. The menu and site maps will automatically adjust accordingly.
Read MoreRotating Banner ads
27 Nov 2013
yes, the site owner can/should be able to change anything. And technically they can as it's all just JavaScript/HTML/CSS. An example is SRL when they publish an article the banner image is placed on the carousel and linked to the article. The page reads this information from the RSS feed.
Read MoreDoes the system have comprehensive error handling and logging?
27 Nov 2013
All web access is recorded in the standard Apache web access logs. The server logs can be configured via log4j All database changes are logged by user and time.
Read More